WebRTC is on the rise, especially after businesses are incorporating video and audio calls on their web browsers and mobile apps. This could be the best news when it comes to establishing sound real-time communication, but with this comes the bad news too, its security-related pitfalls. And, with the number of security breaches happening nearly every other day, it truly resembles a burning daylight in placing confidential information into any video conferencing solution.
So, before entering into the juicy part of how secure WebRTC is, let us see what privacy leaks it handles and how to improve internal communication through WebRTC end-to-end encryption methods.
What is WebRTC Security?
WebRTC or Web Real-time Communication is a profound, flexible streaming protocol, and an open-source technology suitable for offering uninterrupted and bi-directional messaging, audio, and video chats in real-time between browsers and devices.
They are written using JavaScript APIs that help establish P2P (peer-to-peer) communications without the need for any external plugins or interfaces or special integration software.
Plus, the WebRTC protocol is highly liked by the developer community because of its offerings like,
- Low bandwidth and latency – These days all video calling APIs are built with WebRTC to render low latency solutions.
- Seamless audio/video transmission – The data streams, STUN/TURN servers, signaling, and network sockets in WebRTC helps developers to embed audio/video chats.
- Open Source – Anyone can build the app using this open-source technology.
Knowledge Fact: WebRTC works on all major devices or precisely on all internet of things using a WebRTC library.
But, this benefit of WebRTC in being an open source protocol can be a dismay to many, leading to the birth of WebRTC vulnerabilities. And yes, you have guessed it rightly, our next section is,

- Complete Source Code
- Lifetime Data Ownership
- Deploy on Own Server
Vulnerabilities of WebRTC Security
Vulnerabilities mostly referred to “as WebRTC leaks” are not something to be worried about because they are not anything that’s broken or dismantled. Instead, with end-to-end encryption, WebRTC security can turn out to be selling hot pancakes once again amidst the developer bunch.
But, in absence of an encrypted WebRTC, the entire ecosystem falls leading to the compromise of the victim’s identity. This can be a tricky one to solve, and with additional vulnerabilities like the ones discussed below, developers can go erratic while developing applications and businesses would run out of errands in launching new security measures.
- JavaScript injections
- Introducing malwares to WebRTC apps
- Improper session termination
- Absence of certain privileges while installation
- Less secure authentication methods and
- Using signaling server for disclosing information
With WebRTC leaks, should you be worried about its security? That’s our next topic.
Is WebRTC Secure?
Considering the WebRTC security issues, you may ask whether this protocol is really that safe. Without a doubt, yes, it is.
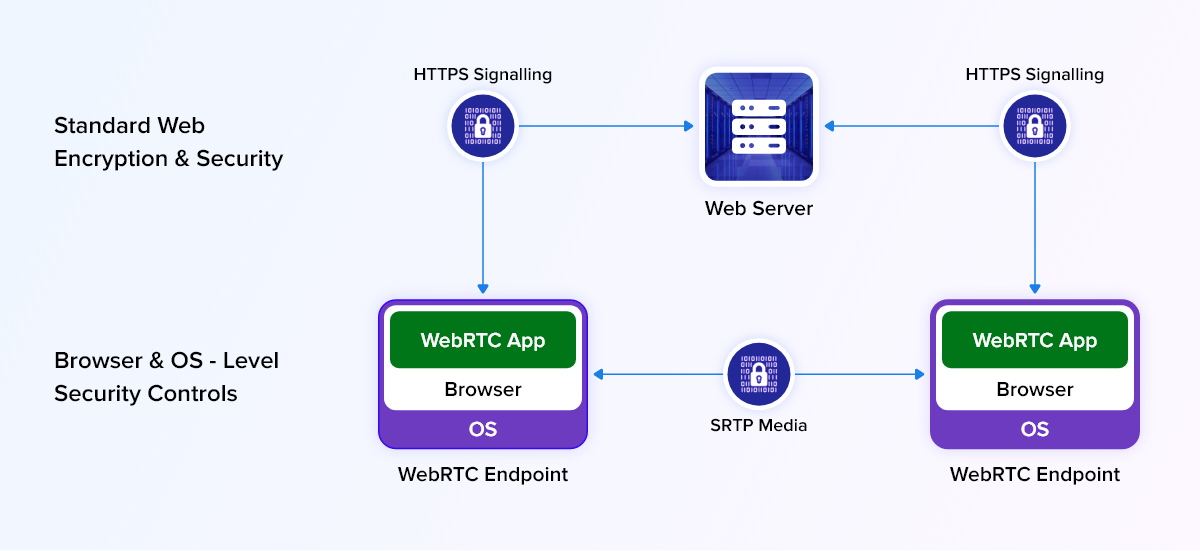
Because WebRTC approaches security from different angles. They come with different encryption specifications like,
- STRP Protocol: For transmitting information through voice, video, or chats between users in WebRTC, the data must be encrypted using SRTP (Secure Real Time Protocol). Using SRTP, the session is encrypted so that without authentication keys, none can decode the message.
- Setting Secure Channels: Not just stopping with encrypting messages, WebRTC sets up secure encryption channels by using key exchange mechanisms like MIKEY, ZRTP, SDES, and DTLS- SRTP.
- Secure Signaling: At the last, WebRTC secures the web servers too that handle signaling and client’s systems using HTTPS protocol – the same protocol that most websites use. This prevents any man-in-the-middle attacks.
What is WebRTC Encryption?

WebRTC Encryption is a means to protect data sent between browsers or apps through WebRTC-enabled connections. Using end-to-end encryption for WebRTC helps protect all the sessions even if any of the connections bypass other security protocols.
Majorly, there are three prime WebRTC security specifications:
- Secure Real Time Protocol (SRTP): It is a secure real-time protocol that encrypts any type of data transmitted across the channel thereby protecting any malicious attacks in this path.
- Encryption Key: This category uses a protocol named DTLS- SRTP requiring keys to transmit data from one peer to another. WebRTC does not make use of other encryption key protocols.
- Signaling: This encryption type locates devices connected over the internet waiting to establish a connection.
Now that we saw how an encrypted WebRTC can help. The next big question remains.
Is WebRTC Encryption Necessary?
To evade all the WebRTC security concerns or issues, adding a layer of encryption is mandatory. Besides this fact, it has become the IETF’s requirement to include the three security specifications mentioned above.
Thereafter, keeping the security and compliance point in mind and going green with the WebRTC encryption is always positive.
The next part that we are going to discuss is a little sturdy and red-blooded one, and your consciousness is very much required.
How Does WebRTC End-to-End Encryption Work?
WebRTC in general has a protocol layer security by default that is controlled by the WebRTC security architecture, and so, developers may not be worried about it too much. However, there are other issues related to browsers and operating systems that could hamper WebRTC connections.
Let us put some light onto the four major WebRTC security concerns of this modern era, starting right with,
1. Web Browser Security
Though this topic is usually not included under WebRTC encryption, still it plays a vital role because these days almost all connections are established through a browser. Therefore, their security has to be monitored closely as they help in securing other supporting connections.
Just like how WebRTC security is mandated by IETF, web browser security standards are also required to be met by the W3C and other internet security specifications. Comparatively to the former, browser security protocols are a bit stringent and order websites to be created with either HTTP or HTTPS connections only.
Their other requirements include granting permission for accessing cameras and microphones on websites, protecting device information, and not allowing sharing IP address information without the user’s notice.
Recommended Reading
2. Operating System Security
Much similar to the browser security protocols, even mobile and desktop operating systems have security protocols in-built that help protects data from malicious attackers. A small hindrance here would be while using mobile devices because different apps for security must be installed from the app store.
You need not worry about the safety of the app because only after strict analysis and tests, the app would have been released.
3. WebRTC Community Security
To be honest in this case, one might think the open-source type of WebRTC can attract many heinous criminals to websites. But that’s not true. Since the code is explicitly available to the public, many would try to correct and improve the code and fix bugs so that any type of security concern is fixed faster than expected.
Similarly, apps that are designed poorly with this technology will receive feedback on how to correct the code and improve the design functionality. This may surely seem counterintuitive, but considering in the long run, it is much better than proprietary technologies.
4. Finally, Protocol Layer Security
As we discussed above the three specifications, SRTP, encryption key, and signaling server form the protocol security club.
- SRTP is used to encrypt any message, audio, or video that is sent across the WebRTC sessions. Here, data will not be compromised as the attacker will not have access to the key.
- Encryption keys are what secures the DTLS- SRTP connection that enables devices and browses connected over WebRTC to exchange encryption and decryption keys. The keys are built with strong codes and are hence difficult to intrude on.
- A signaling server is used by WebRTC to manage all network connections during a session. It is agreed that though WebRTC is a peer-to-peer service, it makes use of a server to find or locate the devices connected over the Internet. It is protected by an HTTPS connection and is pretty much enough for accessing banking and government websites.
That’s it, time to cover up what we discussed.
Conclusion
From learning about the WebRTC security vulnerabilities to taking measures like encryption to protect a connection, we hope we covered almost all the topics that a naive reader would look on for. However, we also suggest you to be in compliance with the security standards to develop or build a secure real-time connection just like how MirrorFly does.
Their video calling APIs are built with secure WebRTC codes that help in offering seamless and low-latency connections on all platforms. If you wish to dive deeper into this topic, take a look at this blog.
Get Unlimited video calling, Fully customizable workflow, Hire a dedicated team & Upload Huge Files
Book a 30 Mins Free DemoTrusted By 500+ Brands
On-Premise Hosting
Full Data Ownership

Frequently Asked Questions (FAQ)
WebRTC (Web Real-time Communication) enables real-time communication features to be easily included in web and mobile applications due to its adaptable and modular architecture. It also involves several key components, as mentioned in the above blog.
- Encryption and DTLS-SRTP Keying
- Identity Protection and Secure Signaling
- Network security with ICE and permission mechanisms
- Media stream isolations
- Security headers and secure data channels
WebRTC (Web Real-time Communication) enables real-time communication features to be easily included in web and mobile applications due to its adaptable and modular architecture. It also involves several key components, as mentioned in the above blog.
WebRTC uses UDP (User Datagram Protocol) to facilitate lower latency in real-time communication. On the other hand, WebSocket uses TCP (Transmission Control Protocol). UDP is primarily used in real-time communication protocols like WebRTC to foster quick and smooth communications.
Yes. WebRTC does mandate end-to-end encryption to safeguard the video, voice, & text data transmitted over the internet between peers. WebRTC makes use of two encryption protocols like DTLS (Datagram Transport Layer Security) and SRTP (Secure Real-time Transport Protocol) to encrypt signaling and media data respectively.
Yes. WebRTC makes use of TLS (Transport Layer Security) for providing security during the initial connection setup between two or more nodes. However, WebRTC does not directly use TLS, rather it uses DTLS which is based on TLS protocol to encrypt the signaling data during WebRTC connection.
SRTP (Secure Real-time Transmission Protocol) is used along with protocols like VoIP and WebRTC. It is a security framework used in order to protect the integrity and confidentiality of the video and voice communications data shared over the internet.
In order to stop WebRTC leaks through unintentional shares of IP addresses in web browsers like Chrome, follow the below-mentioned methods.
- Encryption and DTLS-SRTP Keying
- Identity Protection and Secure Signaling
- Network security with ICE and permission mechanisms
- Media stream isolations
- Security headers and secure data channels
Further Reading
- How video call communication works?
- Top 10 WebRTC API Platforms in 2026
- 20 Essential WebRTC FAQs [Tips & Examples]
- How To Develop A Video Chat App With JavaScript And WebRTC?
Looking for the webrtc app to have video and Voice call for pre-built android apps , looking for self hosting options
Great article about webrtc security. I need an help to build my app, features i required are video chat that should be programmed with WebRTC e2e encryption
Hi its a very good article about webrtc encryption. I am owning a Education center and i just want a demo to with video chat with JavaScript and WebRTC.
Hi i am deepak and i want to make an app for travel ticket booking, My requirement is i need to develop an app with webrtc security. Let me know how to connect with your team
Hey Really happy to say, your post is very interesting to read about webrtc security best practices as well as browser ptotection. You’re doing a great job.
Really great article, which has lots of good information, when someone is in search of what is WebRTC security architecture and its issues.
Very Informative blog! Thank You guys, the article is really helpful. It taught me the more infromation about WebRTC encryption algorithm, webrtc video encryption and webrtc data channel encryption. Thank You for sharing your insights.
Interesting Article. Thanks for the sharing I am also looking for the WebRTC security and encryption standards. I will pin your post. Thanks
Fantastic article. As I would see it, extraordinary explained about webrtc security, srtp cyber security, webrtc encryption protocols, you make everything so easy to understand. Thank you so much. You speak to the very experienced and the professional.
Very useful information and it is well arranged about webrtc end to end encryption, webrtc vulnerabilities, webrtc authentication etc,so it was pretty easy for me to read it. Thanks for the article. Great work!
Good information about webrtc encryption and security standards. The post is well designed and well written. Full of helpful information.