Drive secure instant messaging and video communication with our encrypted chat solution that comes with end-to-end encryption & privacy standards.
Maintain the entire communication system of your platform effortlessly with MirrorFly’s secure messaging platform.
Leverage full freedom to choose where you’ll launch your app - on your own data centers/ private cloud or on MirrorFly’s multi-tenant cloud.
Get lifetime access to control, utilize, and manage all the resources related to your platform, although it’s built on top of MirrorFly.
Tighten app security with 100% end-to-end encryption. Make users stick around conversations confidently with 37+ encryption features, before it’s too late.
With MirrorFly, secure your app in every way, by flexibly modifying the encryption features just as you want!


Let users chat, call and collaborate confidently in your app, without leaving their privacy at stake.
Secure users' personal info anywhere. Whether you host your app on your servers or on MirrorFly cloud.

Enable ultra-fast file sharing, without limiting the size or format, leaving no trace of data behind.
To ensure utmost security, files are divided into smaller chunks and then transferred. That makes it basically impossible for hackers to sneak around.
Privacy is a big deal for us. We never save copies of the files on our servers. Once the transfer's all done, your data gets wiped clean; no traces left behind.
We use a fresh, secure path for every file transfer, with a unique encryption code each time. That blocks any sneaky attempts to intercept or replay your data.
Our secure messaging APIs and SDKs handle all file sizes and types. Just with a hit on 'Send File', the files get delivered smoothly and securely.
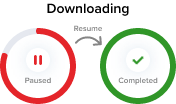
No need to start that download all over again from scratch. Users can pick right back up from where they left off with the resume feature.

Save a ton of your users' time without holding them at their 'File Uploading' status. Enable the exchange of any size of file at blazing-fast speed.
A well-defined architecture for a standardized flow of messages between encrypted servers

Every message & every video call that happens on your app stays compatible with global law enforcement standards and industry regulations.
With APIs and SDKs carefully built to adhere the EU’s privacy regulations, MirrorFly goes the extra mile to protect users personal info.
When it comes to sensitive health info, MirrorFly strictly operates by the HIPAA standards. Drive medical communication with rock-solid security protocols.
Build a secure communication app for the web and protect it from common security threats with OWASP-compatible APIs and SDKs.
Give parents the control to choose what information can be collected on your apps (e.g. gaming/ e-learning) from kids, to ensure child-safety.
Deploy a secure messaging experience across any platform. Protect user conversations on any device (ios & android app) they use to chat or make calls.

Build your privacy-centric secure real-time chat platform with user-specific keys. With Rattlesnake OS, expect security features like verified boot and built it via AWS enabled cloud infrastructure with user-supplied signing keys.
Develop security-hardened, privacy-focused and open-source Android-based messaging applications with ideal features for any purpose of communication. MirrorFly’s encrypted Chat API & SDK supports Graphene OS to improve the security & privacy of the communication.
The predecessor of Rattlesnake OS. Develop a most secure & privacy-focused messaging platform on Android to establish secure relaying of messages at both the endpoints. MirrorFly API supports hardened Android
Build encrypted messaging application on Lineage OS which is open-source and privacy-centric OS for Web and Smartphones. MirrorFly’s SDK/API supports the successor to custom CyanogenMod to develop an application with splendid communication channels (text, voice & video calls).